It's the Boot Loader Dummy
An unverified boot loader fundamentally compromises the hardware chain of trust
3/16/20264 min read
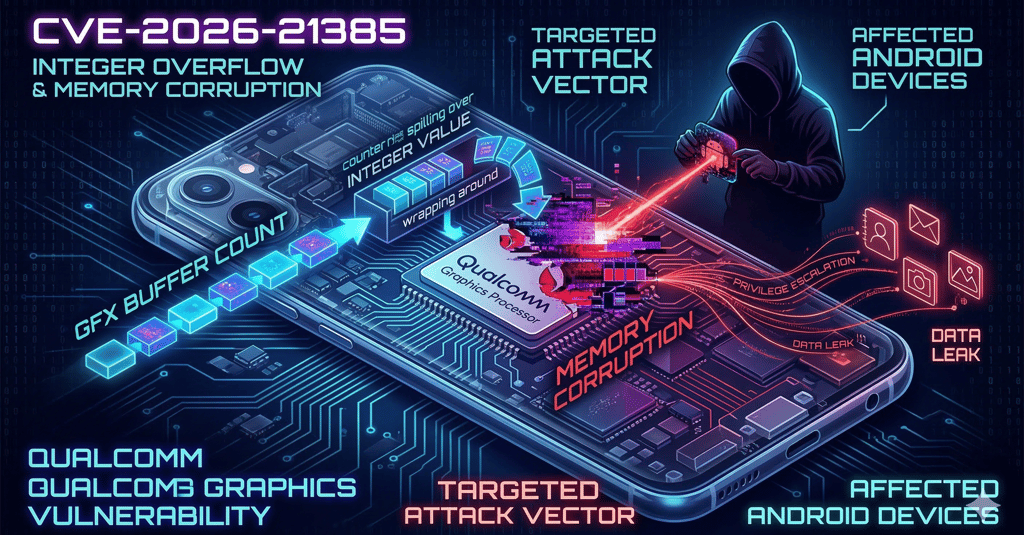
Technical Analysis of CVE-2026-21385
CVE-2026-21385 is a high-severity vulnerability situated within a Qualcomm display and graphics subcomponent. Addressed in Google’s March 2026 Android Security Bulletin, there are confirmed indications that this zero-day has been subject to limited, targeted exploitation in the wild. The vulnerability affects roughly 235 Qualcomm chipsets, expanding its potential attack surface across a vast array of device models and OEM update timelines.
Vulnerability Type: Integer overflow or wraparound.
Impact: Memory corruption.
Execution Vector: A local attacker can exploit this logic flaw to trigger memory corruption within the graphics subsystem. Because graphics drivers require deep interaction with the device kernel and hardware, memory corruption in this subcomponent frequently serves as a highly reliable pivot point for privilege escalation.
Risk Profile: By exploiting this flaw, attackers can completely compromise unpatched systems. This leads to severe organizational risks, including credential theft, unauthorized access to corporate applications, and follow-on intrusion activity if the compromised user account holds elevated privileges.
Mitigation and Remediation
Fixes for this vulnerability were shipped in the second wave of the March 2026 Android Security updates.
Required Patch Level: Devices must be updated to the 2026-03-05 security patch level or higher to be protected against CVE-2026-21385.
CISA Directive: Recognizing the active exploitation, the vulnerability was added to CISA's Known Exploited Vulnerabilities catalog on March 3, 2026, mandating that Federal Civilian Executive Branch agencies apply the necessary fixes by March 24, 2026.
Architectural Risks: Unverified Boot Loaders
An unverified boot loader fundamentally compromises the hardware chain of trust and drastically exacerbates the threat of kernel or driver-level exploits like CVE-2026-21385. When a bootloader executes without cryptographically verifying the next stage of the boot sequence, such as the operating system kernel or low-level firmware. It creates a permanent blind spot in device security.
This lack of verification effectively nullifies established secure boot processes. In a robust, verified boot sequence, the bootloader measures firmware integrity, extending cryptographic hashes into TPM PCR values to attest to the system's exact state before handing over execution control. If a bootloader is unverified, an attacker who achieves local privilege escalation through a graphics driver vulnerability can easily overwrite low-level firmware or implant a persistent rootkit. Because there are no secure boot hashes being validated against trusted TPM measurements at startup, the system cannot detect these deep-seated OS vulnerabilities or unauthorized firmware modifications. This allows an attacker to survive reboots, evade standard detection engineering, and maintain stealthy, persistent control over the hardware layer.
The vulnerability in the Qualcomm Graphics subcomponent highlights a critical intersection between hardware drivers and operating system security. When local privilege escalation flaws like CVE-2026-21385 are exploited, the underlying hardware architecture and its boot validation mechanisms dictate whether an attacker can achieve deep, persistent compromise.
The defense against this kind of firmware or kernel-level persistence fundamentally differs between PC and Android ecosystems.
Bootloader Verification: PC vs. Android
The core difference lies in how trust is established, verified, and handed off during the power-on sequence.
PC Architecture: Measurement and Attestation (The TCG Model) PC secure boot processes rely heavily on the Trusted Computing Group (TCG) standards, utilizing a Trusted Platform Module (TPM). Rather than just checking if code is safe to run, the PC architecture measures the state of the system.
The Process: As the PC boots, the early firmware measures the next block of code (like the UEFI firmware, Option ROMs, and the bootloader) by generating cryptographic hashes.
TPM PCR Values: These secure boot hashes are extended into the TPM's Platform Configuration Registers (PCRs). The operating system or a remote server can later interrogate these PCR values to attest to the exact, uncompromised state of the machine at boot.
Flexibility: If an attacker modifies the bootloader or kernel to maintain persistence after exploiting a driver vulnerability, the resulting hash changes. The TPM detects the mismatch in expected PCR values and can refuse to unseal decryption keys (like BitLocker), effectively halting the compromise.
Android Architecture: Android Verified Boot (AVB) Android does not typically use a discrete TPM or the TCG's PCR measurement model. Instead, it uses Android Verified Boot (AVB), which relies on a strict, cryptographic chain of trust anchored directly into the System on Chip (SoC) hardware.
The Process: AVB uses a "verify-before-execution" model. The immutable hardware Root of Trust (RoT) contains the OEM's public key. The RoT verifies the cryptographic signature of the bootloader. The bootloader then verifies the signature of the kernel, and the kernel verifies the OS partitions (using techniques like dm-verity).
Strict Enforcement: If any stage fails signature verification—meaning an attacker tampered with the firmware or OS image—the device will either refuse to boot entirely or boot into a limited, highly visible "Red State" warning.
Why TCG Recommendations are Not Implemented on Android?
The TCG framework (like discrete TPMs and PCR measurements) is universally applied to PC architecture but absent in Android due to fundamental differences in ecosystem design, hardware constraints, and threat models.
1. Ecosystem Philosophy: Modular vs. Monolithic
PC (Open/Modular): The PC ecosystem is highly heterogeneous. Users build their own machines, swap out motherboards, install third-party graphics cards, and dual-boot entirely different operating systems (Windows, Linux). The TCG standard was created to provide a universal, vendor-neutral way to measure trust across millions of unpredictable hardware and software combinations.
Android (Closed/Integrated): Android devices are vertically integrated, monolithic appliances. The SoC (like Qualcomm or MediaTek), the firmware, the bootloader, and the OS are shipped as a locked-down, unified package by the OEM (like Samsung or Google). Because the hardware configuration is static and controlled, there is no need for a flexible measurement system like PCRs. The OEM simply signs the approved software, and the hardware enforces that signature.
2. Hardware Architecture & Cost
Discrete vs. Integrated: Implementing a physical TPM chip adds cost, takes up physical space on a dense smartphone motherboard, and draws additional power.
Mobile Solutions: Instead of a separate TPM, mobile architectures utilize isolated execution environments built directly into the main processor, such as ARM TrustZone or dedicated security coprocessors (like Google's Titan M). These secure enclaves handle cryptographic operations and key storage internally, achieving the necessary security without the overhead of the TCG standard.
3. The Rollback Problem In a PC environment, updating an OS might change the expected PCR values, requiring the system to cleanly reseal the keys to the new measurements. In mobile, the primary threat is often an attacker rolling the device back to an older, vulnerable firmware version (downgrade attacks) to exploit a known bug. AVB handles this efficiently through rollback indexes fused into the hardware, ensuring that even if an old bootloader has a valid OEM signature, the hardware will reject it if its index is lower than the current device state.